KASTEL (Sicherheit kritischer Infrastrukturen, Sicherheit vernetzter Infrastrukturen)
- Ansprechperson:
- Projektgruppe:
- Förderung:
HGF
- Projektbeteiligte:
KASTEL – Kompetenzzentrum für Angewandte Sicherheitstechnologien
KASTEL - Kompetenzzentrum für angewandte Sicherheitstechnologie, Forschungsprojekt Sicherheit vernetzter Infrastrukturen (SVI), Projekt „Modellbasierte Plausibilitätsprüfung für sicherheitskritische Infrastrukturen des Energy Lab “, PL
In KASTEL arbeitet die Arbeitsgruppe in zwei Projekten mit. Einmal in SVI – sichere vernetzte Infrastrukturen und einmal in SKI – sichere kritische Infrastrukturen. Themen sind ähnlich den bisher genannten: sichere Software, sichere Systemkomponenten, Anomaliedetektion sowie Protokollanalysen.
In der POF IV ist die Arbeitsgruppe im Forschungsbereich Information im Programm „Program 1 Engineering Digital Futures (Supercomputing, Data Management and Information Security for Knowledge and Action)“ aktiv. Hier verantworten wir die Arbeiten des „Subtopic 2 Engineering Security for Energy Systems“ im „Topic 3 Engineering Secure Systems“. Prof. Dr. Veit Hagenmeyer ist hier Principal Investigator.
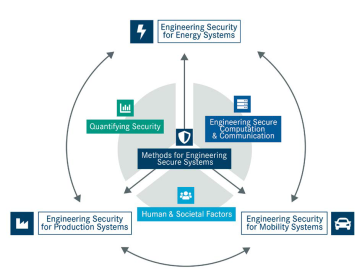
„The main objective of the subtopic is to develop and evaluate concepts, methods, and system technologies (hard- and software) for the secure integration of ICT into energy supply systems with the aim of creating a reliable and secure energy supply. In order to address the communication between the grid participants as well as the application and operational software, a special lab will be set up for energy systems security containing a small smart energy grid model. This model will be used to analyze existing vulnerabilities and possible attack scenarios, including the consequences for the overall grid stability energy supply. For the identified consequences of vulnerabilities, a risk quantification will be applied in cooperation with ▸ Subtopic 1 and adequate countermeasures will be developed and validated. The long-term goal of this Subtopic is to develop methods for a secure and safe example smart grid which demonstrate new approaches and countermeasures that substantially mitigate new risks based on hardened existing software systems.”

